One Identity UNITE User and Partner Conference
We are sorry, the event "One Identity UNITE User and Partner Conference" has already expired.
You may also be interested in.

Modernizing security: Proactive PAM solutions for today
One Identity Cloud PAM Essentials is a SaaS-based privileged access management (PAM) solution that prioritizes security, manageability and compliance.
Read E-book
Securing and managing non-human identities
Non-human identities are essential components of any organizational landscape, yet their security risks are often underestimated. Just like user accounts, they require constant surveillance and protec
Attend Event
Industry Trends and the Importance of Unified Identity Security
Industry Trends and the Importance of Unified Identity Security
Watch Webcast
Integrating SAP Into an Identity Fabric
Watch this webinar to: Understand the challenges and implications of transitioning from SAP IDM to newer SAP solutions. Find out the requirements of identity management for SAP solutions in a variety of environments.
Watch Webcast
AI Powered Identity: Fact or Fantasy?
In a world of deep fakes and AI horror stories, are there any benefits to using AI in something as vitally important as your identity access management (IAM)? One Identity field strategist Robert
Attend Event
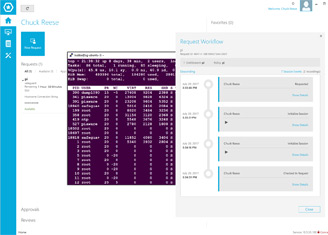
Unleash The True Power Of Safeguard: Privileged Application Auto Logon
Given this level of diversity, it is impossible to find a single PAM solution that supports every system out-of-the-box.
Watch Webcast
The Rise of Identity as a Service as the Cornerstone of Modern Security
Save resources by opting for an Identity-as-a-Service (IDaaS) solution to get everything you need for robust identity management and authentication processes in one solution.
Watch Webcast