[MUSIC PLAYING] Hi. My name is Alvaro Vitta. I'm a principal solutions architect with Quest. Active Directory has been around since the beginning of the 21st century. Over the years, it has gone on a transformation to adapt to changing IT trends. Today, customers are adapting again to the new shift in IT trend, which is cloud. As we move workloads-- As customers more workloads from on-prem resources to cloud-based resources. And Active Directory is coming along for that ride.
There are over 500 million Active Directory accounts worldwide. 90% of organizations across the planet have Active Directory within their enterprises. And they have tied with hundreds and thousands, sometimes, of applications. There are approximately, according to Microsoft, about 95 million Active Directory accounts on a daily basis that are under cyber attack at any given company.
It is difficult to secure Active Directory. Although Microsoft has done a great job in providing great security protocols and great security features and functionality in the native platform, there are still gaps that need to be mitigated. So, for example, it's really hard to understand who's got access to what from a central location. What they're doing with that access. There's really not an automated way to remediate access and recover from security breaches.
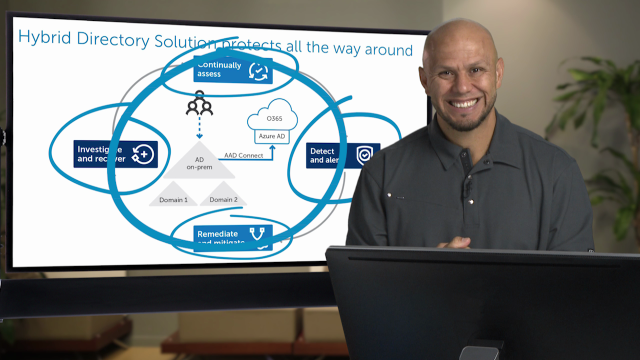
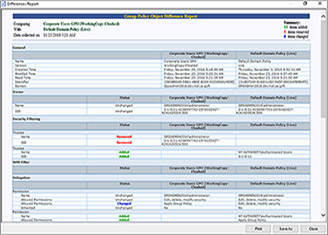
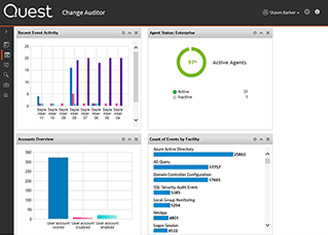
So what should an Active Directory, state of the art security infrastructure look like? You want to first continuously assess who has access to what. Who has access to, for example, backup and recover Active Directory, which essentially makes them domain admins by default? Who has the ability of accessing sensitive files within the organization or log on to very sensitive servers? From there, you want to be able to detect and alert what they're doing with this access, where they're getting access, what changing within the organization, and notify the appropriate people of these sensitive changes that may be occurring within the organization. From there, you want to be able to remediate and mitigate specific actions that may have happened that were unauthorized or mistakes. You want to be able to do it in an automated way.
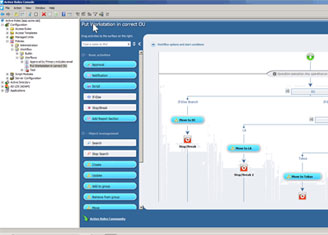
So, for example, if somebody gets added to a group called payroll and they shouldn't be in that group, you want an automated way to automatically remove that person from this unauthorized group and notify somebody about this. And then you want to mitigate this from happening again by having a list privilege access model in place that prevents these kinds of unauthorized actions from happening in the future. From there, you want to be able to investigate and recover. So you want to understand the scope of a particular security breach. Who got affected? What locations, what geography, what servers, what line of businesses in the organization? And then you want to be able to quickly recover from this outage in an automated way.
This is a continuous lifecycle methodology that should protect, on an ongoing basis, your organization because your organization is not static. It's dynamic. It's constantly changing. So you want to constantly be doing this.
In summary, you want to be able to protect Active Directory because of how important and critical it is to the ongoing operations of your organization. You want to be able to assess, detect, remediate and mitigate, and then investigate and recover around either insider threats or external attacks across your infrastructure. Thank you for watching.
[MUSIC PLAYING]
 04:30
04:30