Safeguard for Sudo
Centralized Management and Reporting for the sudoers Policy File
With One Identity Safeguard for Sudo by Quest, you can centralize management of sudoer policy files. This UNIX and Linux PAM tool easily generates reports on sudoer access rights and activities. Additionally, it enables keystroke logging of all activities performed through sudo. The open source sudo project helps delegate the UNIX root account to achieve privileged account management (PAM) objectives. Overcome Sudo’s cumbersome management processes and get compliant.
Key Benefits
Optimize Operations
Improves efficiency and policy consistency with centralized management of sudo across all your UNIX/Linux servers
Simplify Compliance
Quickly provides the Linux PAM information you need with centralized reporting on sudo policy, activities and history
Enhance Security
Increased security with keystroke logging of all sudo activity
Features
Extend Sudo
Leverage plug-ins that extend your current Sudo environment instead of replacing it. Users access the root account the same way they did before there’s no need for additional training minimizing calls to the help desk.
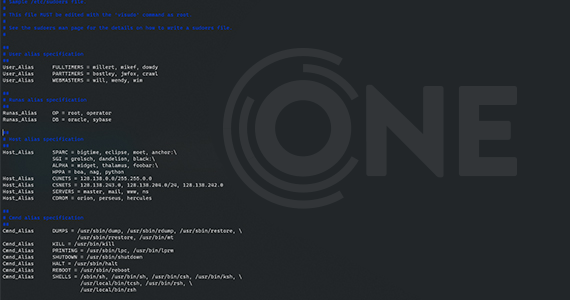
Central Sudo Policy
Use a central service to enforce policy across all of your UNIX/Linux PAM users and servers. This eliminates the need for administrators to deploy sudoers on every system, reducing administrative effort and improving security.
Keystroke Logging
All keystrokes of activities performed through sudo are logged. The keystroke log report is a comprehensive view of the activities and commands that are executed across all systems. You can filter the log report to quickly find the data you need.
Centralized Reporting
Easily track who, what and when changes were made to sudoers, including versioning. Reports analyze the sudo configuration file, user accounts and group memberships. Plus, you can track who ran specific sudo commands across all systems and whether the commands were accepted or rejected. Finally get the UNIX/Linux PAM services you need to secure your environment.
Centralized Management
Use the Management Console for UNIX to manage sudo and other One Identity solutions. This greatly simplifies UNIX/Linux PAM activities and audit-related tasks across your entire environment.
Separation of Duty Enforcement
Using the Management Console for UNIX, you can enforce separation of duties (SoD) and assign users a specific role, which allows them to only execute a defined set of tasks and no more.
Sudo Offline Policy Cache
Provides your organization with service continuity in the event of a network or server outage.
Script Compatibility
Safeguard for Sudo ensures compatibility of your script files that contain embedded sudo commands across your UNIX environment/infrastructure. This allows your organization to avoid run failures and the expense and effort to test and fix scripts.
Specifications
For detailed system requirements and supported platforms please review the latest release notes.
Resources
One Identity Safeguard for Sudo
Extend functionality of sudo with this secure and efficient root access policy management solution
Securely Managing Your Unix Environment
With today’s stringent compliance environment, sophisticated and varied threats, and the demand of interoperability with the fu...
Privileged Management Solutions Simplified
Learn how Privileged Management Solutions from One Identity simplify privileged account management and let you enable super-use...
Hackers have an effective plan to get to your privileged accounts (Government)
How to develop a three-step plan to stop evil doers from appropriating privileged accounts and damaging your agency. One Identi...
AI-powered identity: Fact or fantasy?
Can AI really benefit your identity security? Explore ways this powerful technology can work for you.
The case for unification: Why unified identity matters
As the cyber threat landscape becomes increasingly complex, so does identity management. With fragmented systems and sprawling ...
Ensuring NIS2 compliance with privileged access management: A comprehensive blueprint
The NIS2 Directive is the European Union’s effort to raise the level of cyber resiliency across member states. This paper addre...
eBook: Strategies for successfully managing privileged accounts
One of the most important aspects of an identity security program is the management and governance of the accounts belonging to...
