- Galerie vidéo
- Secure AD with Red & Orange Forests
Secure AD with Red & Orange Forests
 08:19
08:19
Learn how you can secure your Active Directory with Red & Orange Forests.
Show Transcript
Hide Transcript
Welcome, this is Quest Unscripted.
A vlog series on trending topics--
And quest solutions related to Active Directory--
Office 365--
--oh, and don't forget Azure AD.
You're here because you have questions.
We're here because we have answers--
--I think.
We will address questions we've received from customers--
Who experience the same challenges as you.
All with the goal of helping you confidently move--
Manage--
--And secure your Microsoft environment.
We call the show Quest Unscripted because--
Except for the central--
Nothing we say is scripted or rehearsed.
And we're pretty sure you'll notice that right away.
Hello, today I'm joined by Dan Conrad with One Identity, and we're going to talk about red forest, orange forest, green forest, blue. I did a blog on that via quest a few years ago. Dan, what do you know about red forest?
[LAUGHS] I was around during the creation and the invention, and I kind of saw the evolution of why it happened. And I think I understand the intentions of a lot of the red forest scenarios.
So why did it happen?
You know there were some very specific breaches in-- several years ago I guess now. Think time flies. But we started seeing customers ask us questions around, how can I-- do you have any solutions that would mitigate past the hash? And you're like well, wait a minute, why are you asking this? So at that time, that was something that flashed me back to the Windows NT days, and I had to go, honestly, relook that vulnerability and figure out what that was again. And then another customer ask me the same question.
And we started to see that there was this widespread breach, or a well-publicized under the covers breach, that we-- that they were prepping for. And the hashes that were actually living in active director of privileged accounts, the common perspective is as a domain admin, say for instance, as any account in Active Directory, when you log on interactively to a workstation, a server, what have you-- interactively being control-alt-delete, or through RDP-- that the hash is cached in memory to make your single sign on experience better. It's part of the operating system.
When you log off and leave, that hash is still in residual memory. There's specific tools and the hacker techniques of extracting that hash, so guessing passwords whether they're five characters or 500 characters doesn't really matter anymore when they just have the hash. So-- and that's what we started to see was a movement across those.
So Active Directory forest being a security boundary, of course you couldn't go beyond the forest, so that's when we started to see the separation of highly privileged accounts into red forests. And the red forest is just a term, it's because that top level forest in a Microsoft drawing was red, but it's called, what's the-- ESAE enhanced security--
Administrative environment.
--I was going to say agricultural, but that's not it.
And you got to PAWS projects workstation. The yeah--
Yeah.
--secure access workstation. Different people have different acronyms.
Right.
So with that said, I know a big term that's coming up a lot lately, just in time access.
Right.
So I know--
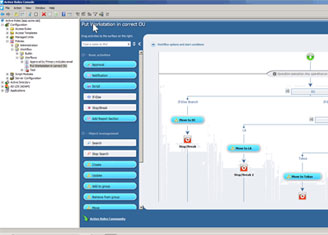
That was something Microsoft came out with, a what they called a PAM solution that was a-- that would actually through FIM workflows and things like that would create accounts on the fly as you need them. So they-- we'll would give them credit for coining the phrase just in time access because the accounts that they would use were created just in time for the use. That seemed a little bit extreme to us, so our version of just in time is disabling the accounts when not in use, and stripping the group memberships when they're not necessary.
Now, didn't One Identity recently add something with Active Roles really to do that just in time access?
Right, so it's with our Safeguard, which is our privileged access management solution so--
Now is that a separate buy, or what's going on there?
It's two separate products that work together, so two great taste that taste great together. So the way it would work is you would take Active Directory accounts, and you would enroll them in the PAM solution. Whether you want to check out passwords, or you simply want to check out sessions to say a domain controller to do a-- play a patch, or whatever it is you're going to do, so you would go to Safeguard and you would check that out. And if you're going to check out the password the account you're checking out has absolutely no group membership other than just the basic domain users group membership.
When I check it out, that account is designated to go into the domain admins group upon checkout, or whatever group you predetermined. So you can have things like workflow approvals and safeguards. So I check it out, maybe my manager, maybe the contract lead, whatever has to approve that. Once it's approved, it's available for me to use. Upon that approval, it'll populate the group membership and act-- using Active Roles to do that.
And then, I go, you know theoretically, go do what I needed to do and then I check it back in. And then when I check it back in, it strips the group membership, changes the password, and disables the account. So it should be utterly useless at that time. Even if I've left residual hashes, they should not be able to authenticate.
Great, we're going to talk about orange forest. I helped coin this concept probably what, 2016, 2017? Dan, I've talked to you about it. From your words, what is-- I want to see make sure I've communicated effectively, and that you can communicate what it is.
Well, when I first heard you say the word orange forest I thought, well, my hunting vest isn't going to be of any value this orange forest. But so it's kind of a hybrid environment where-- and correct me if I'm wrong here but-- in a true red forest scenario one of the things that's recommended is you turn off NTLM, and we haven't found a lot of customers that are actually able to do that. So this gives you that-- it's a lot of the initiatives of the red forest, but not fully engaging the red forest by turning off NTLM authentication.
And just a short plug for Change Auditor version 7.1 that will come out June 2nd, and we can now audit and identify like where NTLM version one's being used, as well as version two. So check out that other video around that. What tool sets are involved in the orange forest that Quest provides?
Well, from the One Identity perspective, around the orange forest you are stepping back a notch from a full on red forest. Is-- a lot of the intended purpose of a red forest can be accomplished probably better than building a very complex architecture and do something like what you call an orange forest, where I can leave NTLM running but I can control how it authenticates, I can control who's using it, and I can even with Change Auditor now, I could even see if I'm even using it.
I love having the workflow approval capabilities as well--
Right.
--so what is it? The four eyes capability? Where one human being can't have sole access to make a change before I make a change. Maybe I want Dan to approve it
Right.
Maybe I don't, but maybe I do.
And that's a good function of GPO Admin. From a GPO perspective, and you look at some of the large Active Directory breaches, especially the ones that where ransomware was spread via GPO, that's a pretty interesting use of a GPO. So I'm a big fan of taking any of the default GPOs, or really any GPO that touches everything. You know honestly, I could say best case try not to have any GPOs behind-- besides a default GPOs that touch everything. Don't let things touch everything.
And those default GPOs that do touch everything, default domain controller's GPO, default domain GPO, lock those with Change Auditor. Set what you need, and then lock them will Change Auditor. So if somebody does breach the environment with a domain admin account or credential, they're still not going to be able to spread ransomware through a GPO. Then take your other GPOs and compartmentalize them, and only apply them where they need to be.
Yup. Yeah, [INAUDIBLE] doing in our security assessment you can go to www.quest.com/securityassessment. We do look at the GPO permissions because [INAUDIBLE] from people. Dan if you remember group policy create owners, you weren't domain admin, you still have right control the different GPOs that you created.
Right, right.
If you're interested, please check that out. And we could maybe show you some different vulnerabilities in your environment. All right. Thanks, Dan.
Produits apparentés
Active Roles
Active Roles est un outil d’administration AD unifié qui sécurise les environnements hybrides et plus encore.
