There’s a new cybersecurity challenge threatening the identity processes and systems of organizations worldwide: identity fatigue.
What is identity fatigue?
Identity fatigue is the result of IT professionals being overburdened by extensive security procedures, ever-evolving compliance requirements and constant security threats. When people get overwhelmed by a sea of work, especially if it’s monotonous, identity fatigue can set in, causing even the most experienced professionals to take the path of least resistance to complete their work. And the easiest path is never the safest. They could end up approving access to an application for someone who doesn’t need it, making an unnecessary privileged account. That means that hackers’ primary targets, privileged accounts, are multiplying by the hour.
Let’s say that a manager has 10 direct reports. Each of the 10 direct reports has 25 applications that they have access to. One day, as part of a scheduled review process, the manager asked to attest if each of their direct reports needs access to the 25 applications. That means that the manager has to review 250 cases. Approving or denying all 250 cases is a lot of work. So, it makes sense that the manager would look for an easy way to save time and get this review process done ASAP. If none of her reports have switched job roles and all their cases seem similar, the manager may be tempted to hit the “Approve All” button. While the manager saved themselves some work, they may have just created 20+ unnecessary privileged accounts, giving hackers that may more ways to infiltrate the organization.
How can identity fatigue be overcome?
The amount of work that needs to be done during identity security reviews isn’t going anywhere. But if you remove the possibility of human error from the equation, you negate the risk of identity fatigue. That’s where Identity Governance & Administration (IGA) technology comes into play.
IGA’s role in overcoming identity fatigue
IGA includes the processes and approvals required to set up, maintain and certify user access to resources your organization needs to operate. (You know, like the example with the manager and their 10 direct reports above.) It ensures that your users only have access to the applications they need to get their work done and only when that access is needed – with the right approval and certification. IGA also automates essential identity governance processes to take the risk of human error out of the equation. Technology doesn’t experience identity fatigue. So, automating review processes means that it will always be done the correct way (and managers can spend the time they would’ve spent approving or denying access on other, more lucrative projects for the organization).
IGA can automate:
- Provisioning: Setting up accounts in a target system to grant appropriate access levels necessary for users to do their daily work
- Workflow: Predetermined, consistent steps to provision and deprovision an account or group membership
- Role management: Includes advanced options such as nested groups or temporal groups
- Account lifecycle management: Using lifecycle patterns to maintain digital identities from creation to archiving
- Access requests
- Access certification (attestation): The periodic review and certification of user access rights
One Identity Manager
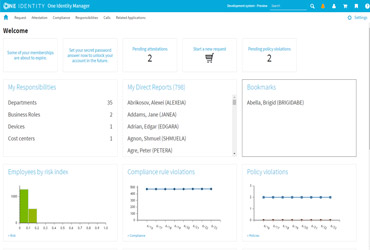
One Identity IGA solution, Identity Manager, is built to deliver identity governance that applies governance across your enterprise. It begins with the basics and foundation your identity security strategy is built on and applies your core processes and approval methods consistently across your IT infrastructure to bring efficiency and compliance to your organization. In short, Identity Manager allows you to:
- Satisfy compliance and audit requirements
- Deploy an identity security model
- Extend governance to cloud apps
- Unify policies to reduce risk exposure
When you put all that together, identity fatigue doesn’t stand a chance.
Don’t let identity fatigue put your organization at risk. Improve your IGA to take human error out of the identity governance equation, improve your user experience, keep your organization compliant and keep your organization’s name out of future identity breach headlines.