Hi,
Currently we have an application that communicates with the 1IM system via the RESTful API provided by the application server. This communication is currently done via the RoleBasedEmployee Authentication Module.
We are looking into changing this so the application uses the OAuth2.0Rolebased Authentication Module.
I have managed to enable the OAuth2.0 authentication module itself, this was easy enough. However the next step seems to be rather unclear in the current documentation. Within designer > configuration parameters > Person there is a parameter called OAuthAuthenticator, followed by many OAuth specific parameters. I know I have to enable this to allow a user to login via the RESTful API using OAuth2.0.
Where I am getting stuck / failing to understand is what I need to get OAuth2.0 working with those configuration parameters.
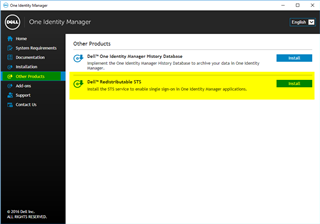
Does 1IM come with an identity provider / service internally for OAuth2.0? Or do we need to implement one / use an external provider such as google etc...?
Any insight or help is greatly appreciated.
Thank you.
Ash