Privilege Manager for Unix
Unix and Linux privilege management that provides centralized control and reporting for root access
Privilege Manager for Unix protects the full power of root access from potential misuse or abuse. No more worries about privileged users deleting critical files, modifying file permissions or databases, reformatting disks, or damaging Unix and Linux systems in more subtle ways.
 02:35
02:35
Learn how One Identity Privileged Management Solutions simplify privileged account management, and let you enable privileged access without putting your entire organization at risk.
Key Benefits
Enhance security
Control root access and enforce least privilege with fine-grained policies
Simplify compliance
Centralize management and reporting for compliance and visibility
Increase accountability
Record user activity with automated, secure keystroke logging
Features
Unix delegation
Enable Unix and Linux privilege management through detailed, policy-based delegation of Unix/Linux root account privileges.
Keystroke logging
Record the user’s keystrokes and the terminal output of any sessions granted by Privilege Manager for Unix.
Event logging
Record details of all requests to run privileged commands, including who made the request, when and where it was made, and whether it was accepted.
Encryption
Guard against network snooping and spoofing by encrypting all communication among Privilege Manager for Unix programs, and between the user and application.
Transparent operation
Use Privilege Manager shells to audit and control a user’s login session in a way that is transparent to the user regardless of how they are logged in.
Capabilites
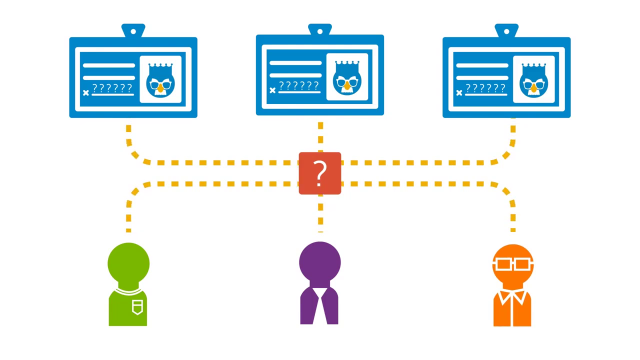
Role-based root and administrative account delegation
The product supports Unix and Linux privilege management by enabling you to delegate root-account administrative privileges based on individual roles and rights, without revealing the root account credentials. Plus, with Privilege Manager for Unix you can easily handle third-party applications management, including Oracle and SAP.
Comprehensive policy creation and testing
Privilege Manager for Unix enables you to import third-party policies, as well as build new policies based on user, groups, commands, hosts, time of day, day of the week — and test the impact of those policies before pushing to a production environment.
Secure centralized management
Configuration and management are delivered through a GUI and/or via command line. The architecture is fully fault-tolerant with failover and load-balancing options. Moreover, Privilege Manager for Unix encrypts its network traffic and integrates with Pluggable Authentication Modules for increased security.
Indelible audit trail
As part of complete Unix/Linux privilege management program, you can track who has been accessing which systems, what commands they executed, what changes they attempted to make to key files and data, and whether those changes were successful.
Encryption, authentication and program controls
For greater security, Privilege Manager for Unix encrypts network traffic and prevents the storage or execution of unauthorized or destructive programs on your Unix systems.
Central management of heterogeneous networks
You’ll enjoy a single management interface and full functionality for your multi-platform/OS environment, including IBM AIX, HP-UX, Sun, SuSE Linux, RedHat Linux, and more.
Specifications
For detailed system requirements and supported platforms please review the
latest release
notes.
Resources
Securely Managing Your Unix Environment
With today’s stringent compliance environment, sophisticated and varied threats, and the demand of interoperability with the fu...
The 12 Critical Questions You Need to Ask When Choosing an AD Bridge Solution
AD bridge solutions address this problem by enabling Unix, Linux, and Mac OS X systems to participate as “full citizens” in Act...
Learn how to enable privileged management with One Identity solutions
This video will show you how to centrally manage privileged accounts, using the policy-based workflows provided by One Identity...
Privileged access is the new shadow IT (and it’s lurking in your organization)
Privileged access is the Wild West of identity. But you can turn it into a locked down system with One Identity PAM.
The case for unification: Why unified identity matters
As the cyber threat landscape becomes increasingly complex, so does identity management. With fragmented systems and sprawling ...
AI-powered identity: Fact or fantasy?
Can AI really benefit your identity security? Explore ways this powerful technology can work for you.
Lessons learned from a year of identity compliance upheaval
The growing number of cybersecurity regulations makes compliance difficult. Setting up IAM will help, along with the insights f...
Unified hybrid Active Directory
Managing on-prem AD is hard enough, but when you throw Azure AD into the mix things can get out of control quickly. This eBook ...
