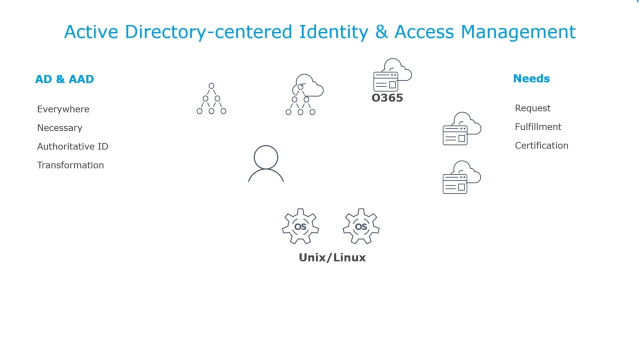
An AD-centered approach to enterprise IAM
 08:48
08:48
Related videos
One Identity keeps threats at bay for the University of Cyprus
Explore the benefits of One Identity Manager in the field of education with Despo Othonos, IT Systems Administrator at the University of Cyprus. One Identity...
06:26
ESS Eric automates IAM and the identity lifecycle with One Identity
The European Spallation Source Eric maintains comprehensive IAM with One Identity Manager – from start to finish. Join Rikard Krisle, Product Manager and So...
05:47
Mark your calendars: One Identity UNITE comes to Chicago in 2026!
Don’t miss the opportunity to join industry experts, partners and peers in Chicago for the 2026 UNITE customer and partner conference. Imagine a sellout conf...
00:23
Identity Manager: Proven and Trusted IGA
Learn the unique value that One Identity Manager provides to companies looking for an IGA solution to streamline their identity management while protecting thei...
03:03
One Identity approach to AI in cybersecurity
Larry Chinski, VP of Corporate Strategy at One Identity, explores the dual nature of AI in cybersecurity, highlighting how the company leverages predictive AI t...
03:20
Mark your calendars: One Identity UNITE comes to Vienna in 2026!
Don’t miss the opportunity to join industry experts, partners and peers in Vienna for the 2026 UNITE customer and partner conference. Imagine a sellout confe...
00:26
Unifiez et sécurisez votre IAM avec One Identity Fabric
Découvrez comment One Identity Fabric connecte vos solutions de sécurité des identités dans un écosystème unifié, renforcé par l'IA pour permettre des analyses ...
00:45
Unifique y proteja su IAM con One Identity Fabric
Descubra cómo One Identity Fabric conecta sus herramientas de seguridad de identidades en un ecosistema unificado, mejorado con IA integrada para obtener inform...
00:45
Vereinheitlichen und sichern Sie Ihr IAM mit der One Identity Fabric
Entdecken Sie, wie die One Identity Fabric Ihre Identitätssicherheitstools zu einem einheitlichen Ökosystem verbindet, das mit integrierter KI für prädiktive Er...
00:45
Unify and secure your IAM with the One Identity Fabric
Discover how the One Identity Fabric connects your identity security tools into a unified ecosystem, enhanced with built-in AI for predictive insights, early th...
00:45
The future of digital identity: DNA, AI and blockchains
Privileged Access Management Strategist at One Identity, Alan Radford, explores the potential of DNA-based identity verification through blockchain technology a...
05:12
Managing identities in a growing organization: Lessons from SECURA Insurance
Joe Albers, Senior Information Security Engineer at SECURA Insurance, shares how effective identity management is crucial for compliance and security in the ins...
05:00
CEO keynote - The market is screaming for consolidation
Listen to Mark Logan, CEO of One Identity on the future of the identity fabric.
04:09
AWI trusts One Identity Manager to protect 50 years of scientific data
Andreas Thiele from the Alfred Wegener Institute (AWI) shares how One Identity Manager has streamlined the organization’s processes and improved security for th...
04:02
CEO keynote: Mark Logan - State of the Business
Listen to Mark explain the future vision of the organization and hear why we're the identity security company to partner with.
03:49
