[MUSIC PLAYING] Hello, everyone, and welcome to this fireside chat with Forrester and One Identity. This is the second part of our conversation with Forrester around the renaissance that we see around the zero-trust approach to security. So today, we're going to review some of the core tenets of zero trust, examine some misconceptions that have taken root in the decades since Forrester first introduced concepts.
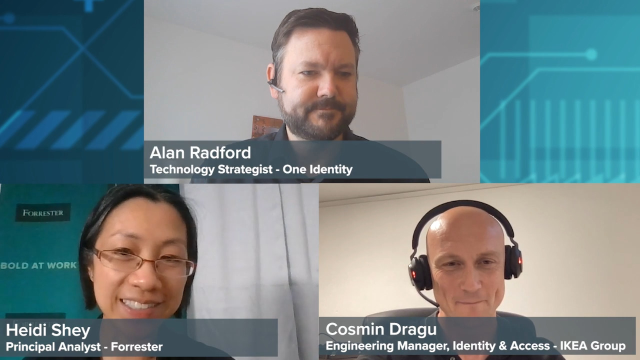
My name is Alan Radford. I am a Technology Strategist here at One Identity, and I'm very pleased to be joined here today by Cosmin Dragu, who is an Engineering Manager for Identity and Access Management at IKEA Group, who we're very pleased to have as a customer of One Identity. Cosmin, welcome today.
Thank you.
And also from Forrester, we have Heidi Shey. Heidi is Principal Analyst. Her research focuses on data security and privacy strategy. And she helps guide clients in applying zero-trust, data-centric approach to securing data. Heidi, welcome to you as well.
Thank you.
So let's kick things off. I'm just going to come straight into it and mention that 2009, I think, is when Forester first introduced the concept of zero trust, which a phrase that always stuck in my mind is that it was based on a realization that traditional security models operated on the outdated assumption that everything inside an organization's network should be trusted.
And given, in 2009, that was an outdated assumption, I think we can all agree our viewers included that the world has moved on since then. Digital transformation is in full swing and ongoing. And really, that leads to what are the common misconceptions around zero trust that we need to be bearing in mind on this digital journey that we're all on, Heidi.
I think so because I think, originally, we thought about this trusted versus untrusted network. And a lot of the focus early on with zero trust was really about, I think, how we thought about the network and things like network segmentation and taking away this notion of trust. And that's still something that I think continues on today.
Sometimes we run into these misconceptions that it's still very much focused on the network and network security. And it's still a core concept, but zero trust as a concept has evolved to something that's much broader than that. It's a whole framework. It's a whole ecosystem of controls and integration these days.
And I'd like to bat that same ball over to you, if I may, Cosmin. What's your take on zero trust and some of the misconceptions you've encountered?
Well, first of all, I would like to say that I see myself, and IKEA as well-- we see it as a more dynamic environment which we're transforming into. And so that dynamic environment requires dynamic thinking. And so we cannot really-- it's difficult to attack that problem in a static way like we used to with static rules and static roles and static access. We need to think beyond that, having an ever-changing, iterative approach to this dynamic environment.
So before I come back to Heidi, let me drill down into that a bit more, Cosmin, if I may, because I'm hearing dynamic. I'm hearing a need for not static. In the conversations we've had with customers from One Identity's perspective, there's users in motion. There's applications in motion. There's data in motion. And all of it is being virtualized in cloud, automated as a huge amount of elasticity across all of those entities.
And so the need for the policies themselves to be dynamic, as you allude to, has become so important across the whole cybersecurity ecosystem. And so I'd be keen to get an understanding of what some key challenges that you've observed, Cosmin, perhaps in how IKEA have responded to this concept and how you approach zero trust from your perspective.
Yeah, sure. I guess one example would be how we think about data and how do we use data analytics, correlation of logs, policy engines, machine learning to be able to take fast and good, appropriate decisions based on this context switching, if that makes sense. That's one of the key concepts there for us at IKEA.
Secondly, I would like to point out the importance of having a great or good leadership that can translate these concepts into actionable items, as I would like to put it. We can talk a lot about zero trust. We can talk around points and boxes and arrows. To be honest, we can do that all day.
But at the end of the day, we have to move. We have to do something. And for every day that we wait, we kind of lose an opportunity to move the needle in the right direction, so to say. So the ability to execute in an iterative approach is very, very important to us.
So I'm hearing high frequency of switching of context and needing to keep on top on an ever-changing context, the ability for leadership to translate these inputs into actionable items and then execute against those actionable items. Heidi, may I bat that over to you and, in so, sort of reiterating the question around some challenges around organizations have responded to this concept? How does what Cosmin say resonate with yourself?
I think one of the key things that Cosmin was talking about here was that that iterative approach, the translation into action-- this all points to one of the common challenges that we see, and I think also may be one of the myths that we encounter as well, where people assume that this is-- zero trust, it's a project. You do it. You're done.
But, no, it's certainly not the case. It's iterative. It's a journey with this approach that you take. And there may be some quick wins that you can get immediately in terms of actions that you take. Sometimes we see that in the form of companies enabling multifactor
 43:53
43:53
