One Identity Safeguard Privilege Manager for Windows
Comprehensive least-privileged administration and application control.
Help your end users elevate and manage their own user and administrative rights while maintaining a least-privilege,
GDPR-compliant environment with One Identity Safeguard Privilege Manager for Windows. Leverage pre-packaged and community
elevation rules to address the most common needs. Applying the elevation rules is more effective with the integration of Quest’s patented and
powerful Validation Logic targeting technology. Privilege Manager works seamlessly with Active Directory and Group Policy Objects. You won’t find an
easier or more affordable way to maintain security while allowing users more self-help capabilities in a locked-down PC environment. One Identity Safeguard
Privilege Manager for Windows is easy to deploy and manage.
Self-service
Allow end-users to easily elevate and manage their own user and administrator rights, while maintaining a least-privileged environment.
Automation
Avoid the pain of managing each user and desktop individually by automatically elevating permissions with privilege elevation rules.
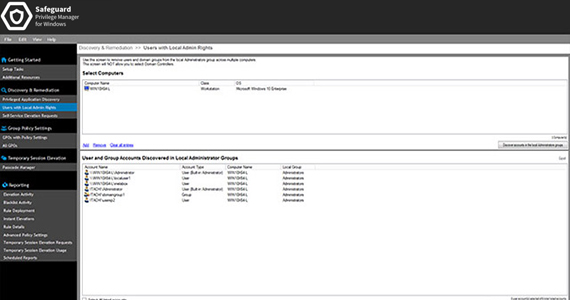
Visibility
Discover applications that require administrative privileges and apply pre-defined privilege elevation rules.
Flexibility
Delegate privilege management responsibilities to OU-level admins in organizations of all sizes.
Security
Control user-level access to unwanted or suspect applications.
Integration
Seamlessly integrate with Active Directory and Group Policy Objects.
Key Features
Elevation on-demand
Take advantage of myriad options for end-user admin access to optimize productivity and security.
Digital certificate verification
Save time by automatically elevating all the applications from a specific publisher
Validation Logic
Use our Validation Logic technology to target access rights to any combination of users, user groups, platforms or applications.
Reporting
Stay apprised of what’s happening on your Windows desktops with reports that provide a quick and simple status of elevation and rules activity.
Community rules exchange
Maximize your investment by using or adding to the more than 100 pre-existing rules in the Community Rules Exchange.
Blacklisting
Deny user access to unnecessary or unwanted applications for increased security and efficiency.
Specifications
Operating systems
- .NET Framework 4.0
- PDF reader to open the Privilege Manager guides
- Microsoft Group Policy Management Console
- Screen resolution of 1024x768 or higher
- Windows Server 2008
- Windows 7 Enterprise, Professional, or Ultimate Editions
- Windows Server 2008 R2
- Windows Server 2012
- Windows 8.1
- Windows Server 2012 R2
- Windows 10
- Windows Server 2016
- Windows Server 2019
Resources
Privilege Manager for Windows
How to Get Privileged Access Management Right
Watch this video to learn how a holistic and comprehensive approach to PAM can help you reduce risk, increase security, and bet...
Eight Ways to Analyze Privileged Sessions to Identify Your Most Suspicious Activity
Watch this Randy Franklin Smith-hosted webcast on demand to learn about the eight ways that you can analyze privileged activity...
Learn Five Reasons to Invest in Next-Gen Privileged Access Management
Are you still using traditional privileged access management (PAM) solutions – or don’t yet have an effective PAM strategy? The...
KuppingerCole White Paper: Enhanced Privilege Access Management Solutions
PAM is critical to mitigating risk and securing your organization. Keeping up with the rapid pace of change is difficult. But i...
2022 Identities and Security Survey Results – Understanding The Challenges Fragmented Identity T...
Read survey to learn more about how Identity security is quickly emerging as a top priority to help organizations improve their...
2020 KuppingerCole Leadership Compass for Privileged Access Management
Overview of the market for Privilege Access Management (PAM) and review of vendor solutions
KuppingerCole has positioned One Identity as a Leader in the Leadership Compass for Privileged A...
Privileged Access Management (PAM), over the last few years, has evolved into a set of crucial technologies that addresses some...
Get started now
Straightforward and effective Windows privilege management
